At Kloudbean, database access is secured using a robust firewall system designed to restrict unauthorized access. By default, all public access to your databases is blocked to ensure that only trusted sources can connect. This system allows you to whitelist specific IP addresses from which you expect traffic, such as your application servers. For scenarios where temporary access is needed, such as development work from a local machine, you can open public access on a short-term basis, ensuring that it is restricted once the task is completed. This approach gives you fine-grained control over who can access your database while maintaining a high level of security by limiting exposure to only trusted IP addresses. With Kloudbean’s firewall system, you can confidently protect your database from unauthorized access and reduce potential vulnerabilities.
Database Access Management on Kloudbean
At Kloudbean, we understand that database access is one of the most critical aspects of your infrastructure’s security. Since your database contains sensitive and valuable data, it is essential to have stringent access controls in place to prevent unauthorized access and potential data breaches. As a result, Kloudbean takes a strong stance on limiting access to your databases and encourages the best security practices when it comes to managing database access.
Default Access Settings
By default, Kloudbean disables all database access to ensure the highest level of security. This approach minimizes the risk of unauthorized access and ensures that no one can access your database without your explicit permission. This strict control is part of Kloudbean's commitment to providing a secure and reliable environment for your data. With no access granted by default, your data remains protected, and you are in complete control over who can access it and when.
On-Demand Access
Access to your Kloudbean database is granted on-demand, meaning that you can enable access only when needed. This gives you complete control over who can access your database and for what purpose. Whether you’re performing administrative tasks, running queries, or troubleshooting issues, you can choose to allow access temporarily, ensuring that access is given only for the duration of the task.
Security Best Practices for Database Credentials
Another important aspect of securing your database is how you manage your database credentials. Kloudbean strongly discourages sharing your database credentials via insecure channels, such as email or unencrypted messaging platforms. Sharing credentials in this way can lead to them being intercepted by malicious parties, potentially giving unauthorized individuals access to your database.
Always use secure channels to communicate credentials, such as encrypted messages or password managers designed for secure sharing. Additionally, never share credentials with individuals who do not absolutely need them to perform their tasks. Limiting access to credentials is an essential practice in maintaining the confidentiality and integrity of your data.
Steps to allow Database access
1: Go to Database Administration
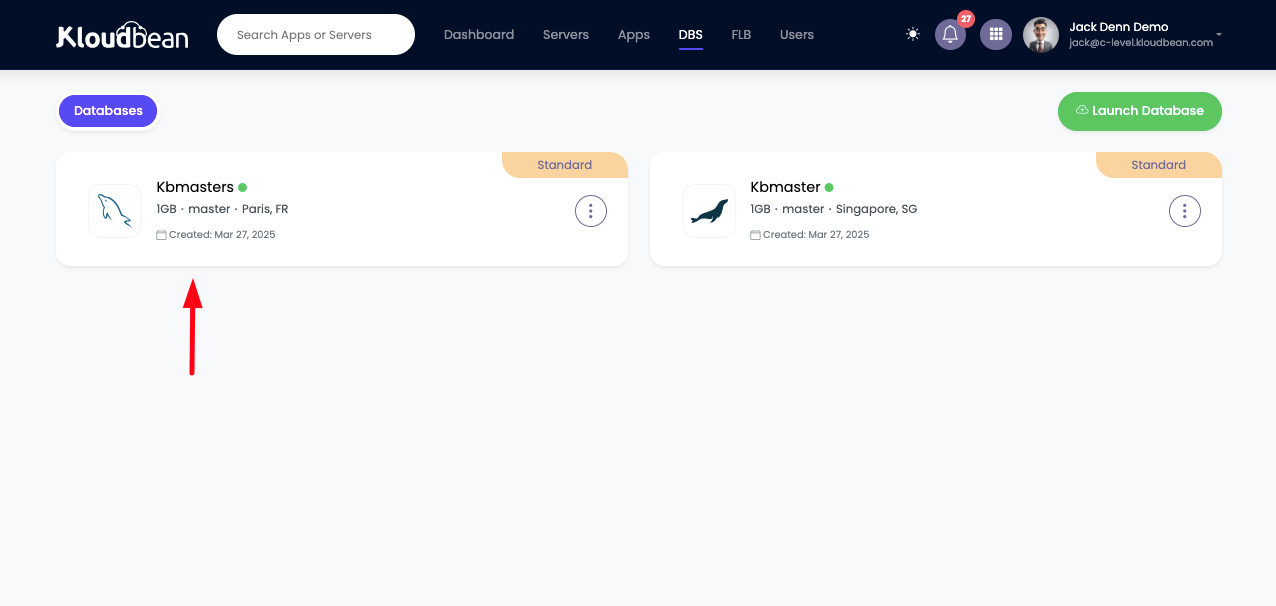
From the dashboard click on Managed Database to go to DBS (Database System) section to view existing databases.
Clicking on your database, It should take us to databases Administration section.
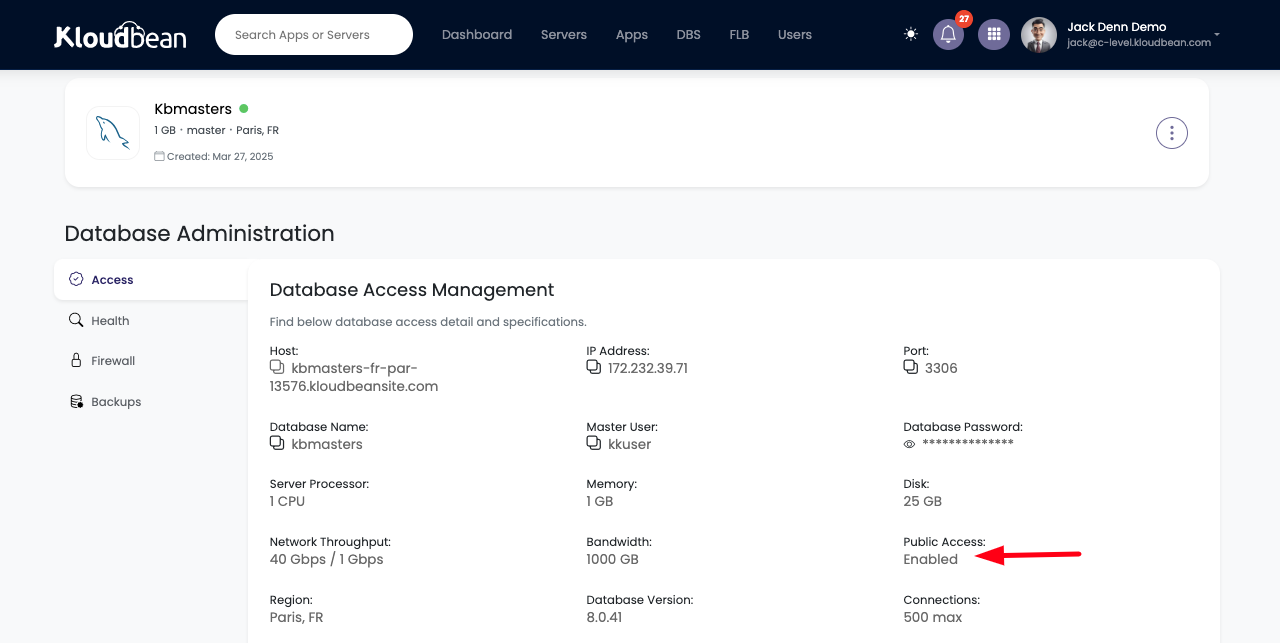
Once you are in Databases Administration. You see following field in Access tab.
Public Access: This field represent our current settings for the database, as of now our database is not accessible from anywhere, until we update database access from Firewall section.
Currently public access is completely disabled.
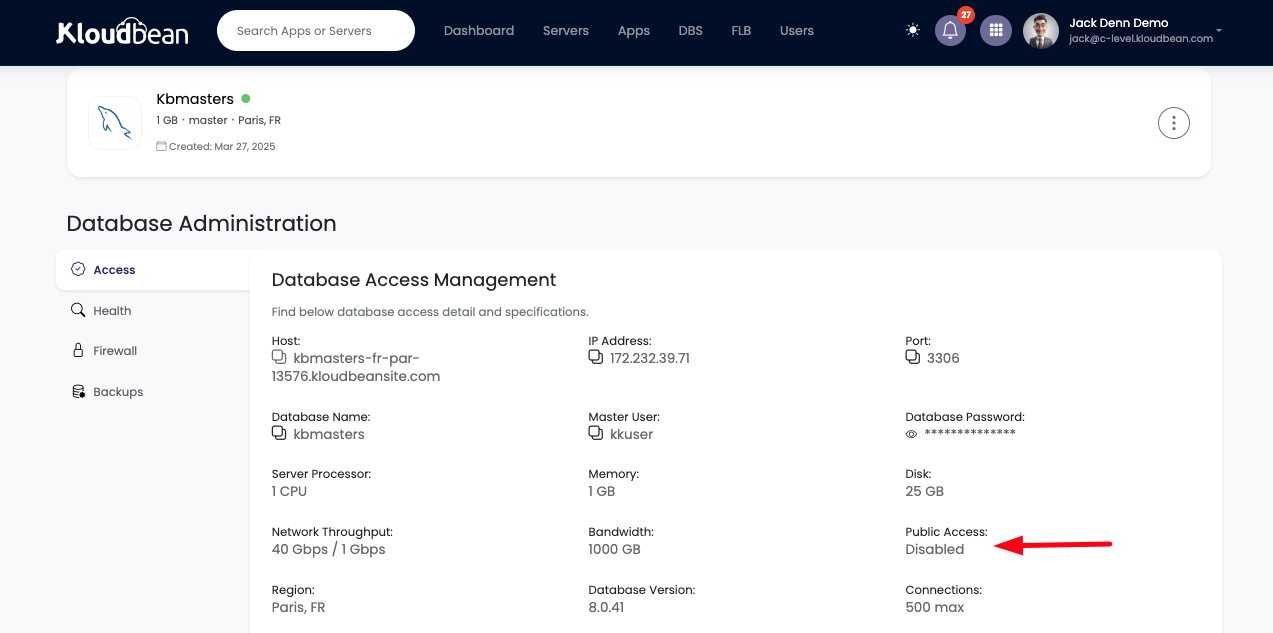
Which means as of now no one is able to access the database. Let's go ahead and see how we can enable access.
2: Whitelist required IP addresses for database access
A more secure and recommended approach is to allow access only from specific, trusted IP addresses. This is particularly useful for ensuring that only known servers, such as your application server or company proxy server, can connect to your database. This method drastically reduces the potential for unauthorized access because only requests originating from authorized IPs will be able to communicate with your database.
By restricting access to specific IPs, you can significantly enhance the security of your database. For example, if your company has a dedicated application server, you can whitelist the IP address of this server, ensuring that only requests from that server are allowed. This tight control over access is far safer than enabling open public access, as it helps mitigate the risk of attackers or unauthorized users connecting to your database.
We are going to see how to allow access only from particular IP addresses from where application is going to access it.
Go to Firewall section.
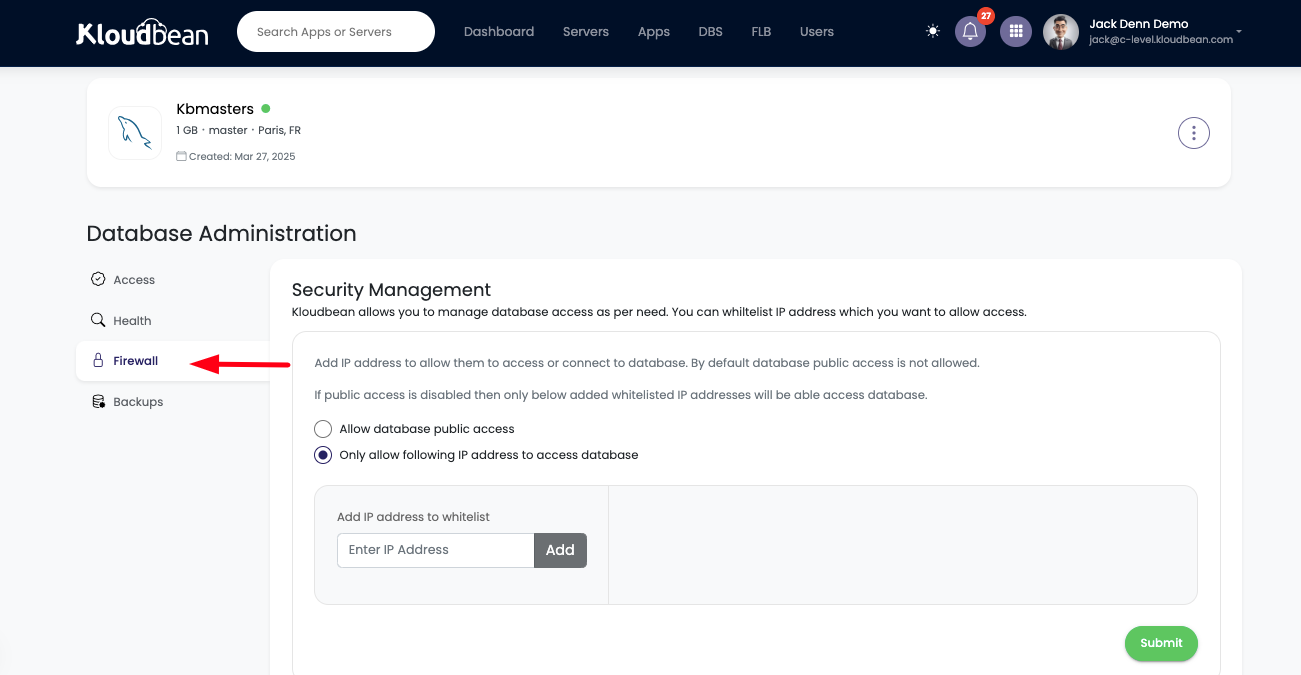
For Firewall section choose following option ;
"Only allow following IP address to access database".
Add the IP address from where you want to allow access, we can add multiple IP Addresses as per demand.
3: Add desired IP addresses for database access
Just insert IP Address and click on Add button. Add as many IP address as you to allow access from.
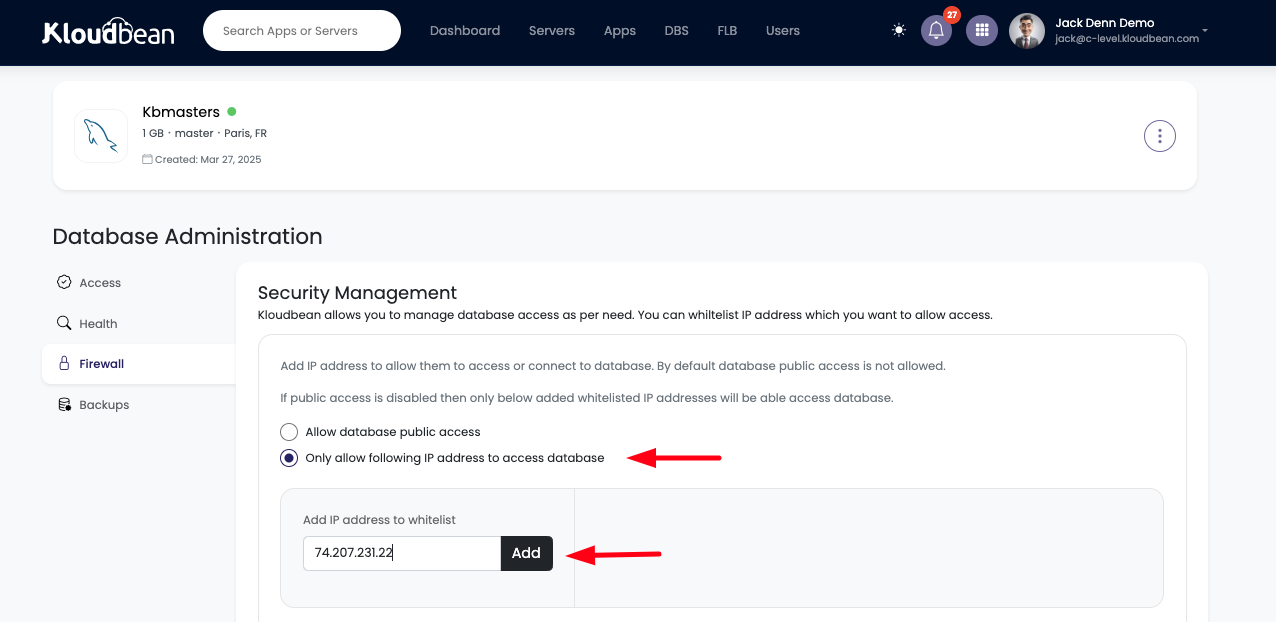
Once added, click on Submit button to whitelist these IP addresses.
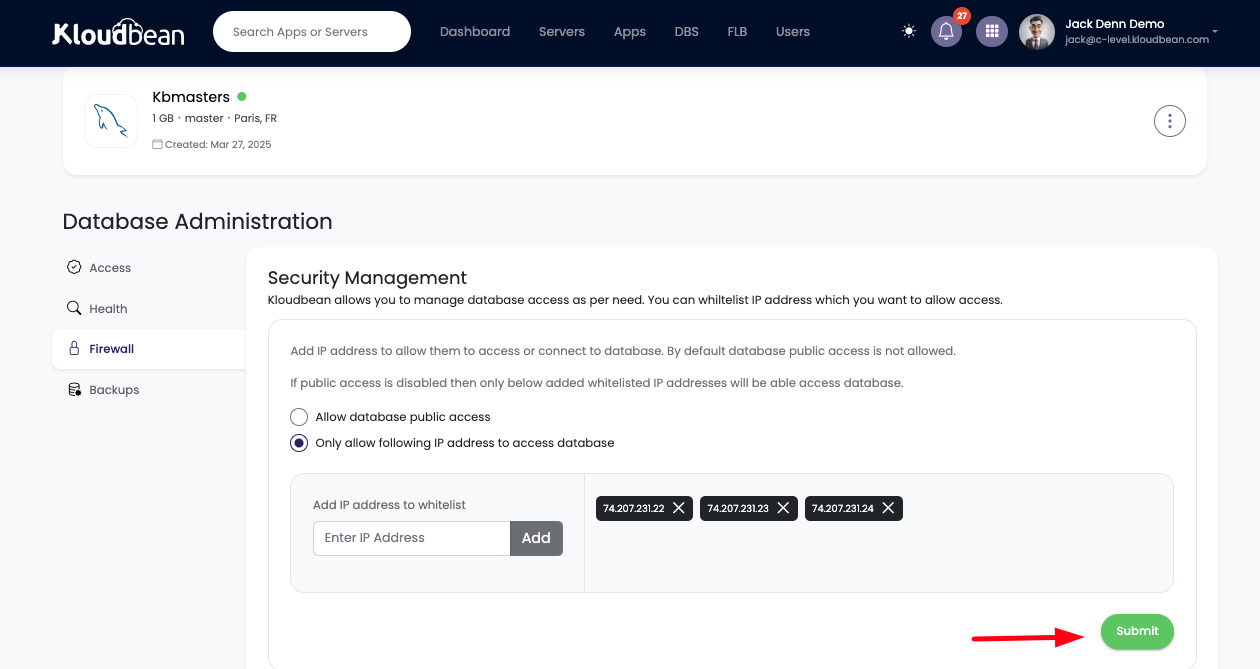
As the mentioned IP address has been whitelisted, now we should be good to access database from this particular server.
Allow Public Access – A Temporary Solution
While Kloudbean does allow the option to enable public access, this should only be used in very specific cases, such as during development or troubleshooting. Public access should be enabled only for short periods, and once the task is completed, it must be disabled immediately.
Kloudbean strongly discourages keeping public access open for extended periods due to the security risks it poses. Public access increases the chances of unauthorized individuals gaining access to your database, leading to data breaches, potential misuse, and security vulnerabilities. For this reason, public access should be treated as a temporary measure and should be shut off as soon as it is no longer necessary.
If we want to access database from our local machine by using any tool, we have to enable public access.
However, enabling public access is not recommended under normal circumstances and should only be done in specific cases where temporary access is needed. In such cases, public access can be enabled for a short period, such as when making changes from a local machine, and should be promptly disabled once the necessary tasks are completed.
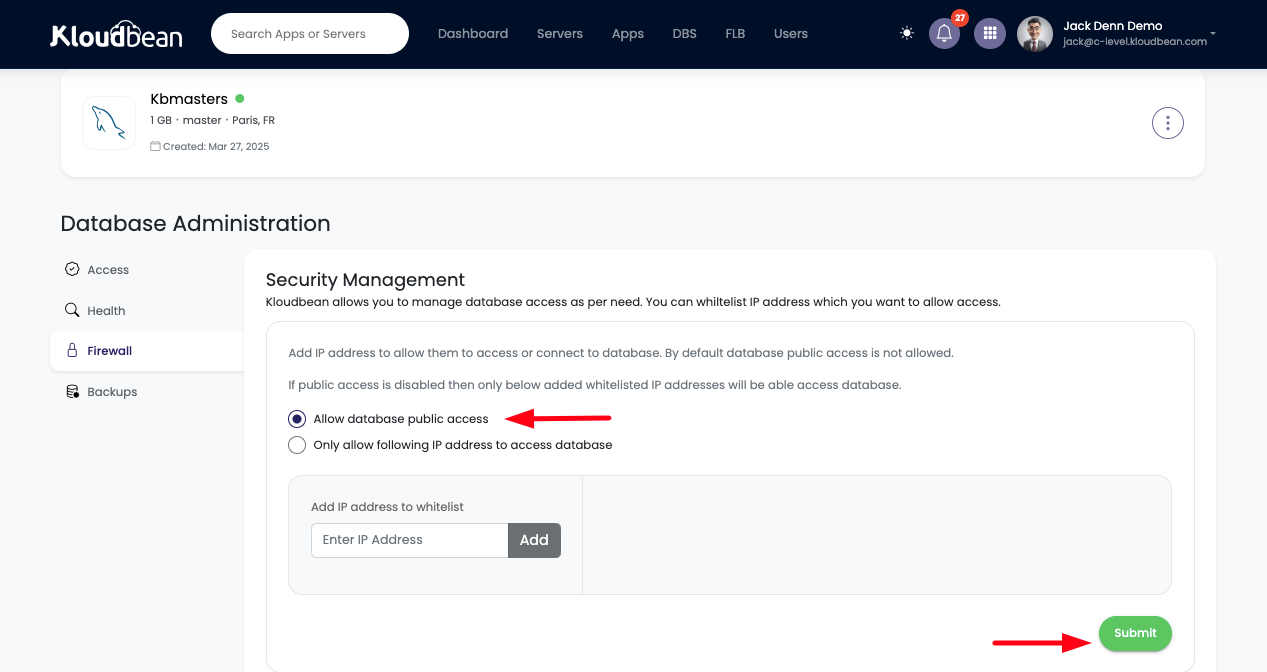
To enable public access follow these steps;
Go to Firewall section
Select the following option,
"Allow database public access"
And hit Submit button.
This should turn on database public access.
We can check current Public access status from Access tab.
This time Public access is showing Enabled. Which mean database is publicly accessibly.
However we can disable public access again from Firewall section
When to Rotate Database Credentials
Rotating your database credentials is a critical security measure that helps prevent unauthorized access in case your credentials are compromised. Here’s when you should rotate your credentials:
- When You Suspect a Compromise: If you believe your credentials have been compromised—whether through an insecure sharing method, a breach, or a leak—you should immediately rotate your credentials. This is a crucial step to ensure that unauthorized parties cannot access your database and potentially cause harm.
- Immediately Disable Access or Contact Support: If you suspect that your database credentials have been exposed or are at risk, it’s important to act quickly. First, disable access to your database to prevent further unauthorized attempts. Then, contact Kloudbean’s support team for immediate assistance in rotating your credentials. We can help you quickly change your database credentials to prevent any security leak or data theft.
Proactive Security Measures
It’s also essential to practice good password management by using strong, complex passwords for your database credentials. Avoid using easily guessable passwords or reusing passwords across different systems. Regularly updating and auditing your credentials can help you stay one step ahead of potential threats. Furthermore, enabling multi-factor authentication (MFA) wherever possible provides an additional layer of security to prevent unauthorized access.
Conclusion
At Kloudbean, database access is a key component of your overall security strategy. To ensure that your data remains safe and protected, we take several measures to limit access to your database. By default, access is disabled, and you can enable it on-demand when necessary. We recommend granting access only from specific, trusted IP addresses and strongly discourage public access due to the inherent security risks. Additionally, securely handling and sharing your database credentials is essential for maintaining the confidentiality of your data.
In case of any security concerns, always rotate your credentials immediately. If you suspect a compromise, disable access and contact Kloudbean support for assistance in quickly rotating your credentials and securing your data. Following these best practices will help ensure the integrity of your database and minimize the risk of unauthorized access. With Kloudbean’s robust security measures, you can confidently manage your database access while keeping your data safe.
If you encounter any issues while managing database access on Kloudbean, our expert support team is available 24/7 to assist you.